Training & Coaching
We offer training and coaching in systems-based, people-powered advocacy for changemakers seeking greater impact. We have two public trainings coming up...
Brazil PT Webinar
O treinamento será realizado em formato on-line, com duração de 2 horas para até 50 participantes, no dia 20 de março de 2024, com base em nosso Treinamento sobre fundamentos de campanhas modernas.
Campaign Accelerator Training Berlin
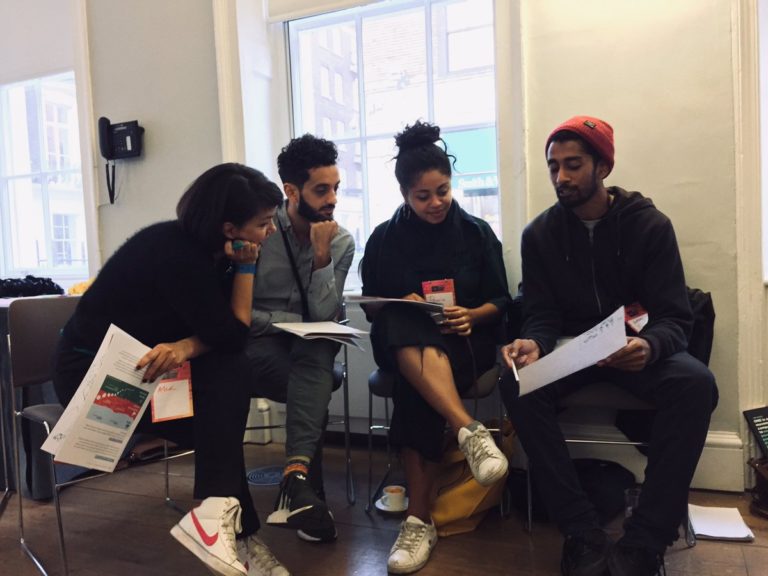
This is a dynamic process. We brainstorm and experiment. We interact with our key audiences. We work together across disciplines and expertise, welcoming diverse perspectives.
Planning a campaign?
We facilitate workshops that result in creative and collaborative plans.
Want to inspire action?
We organise trainings on the essentials of engaging and effective digital-era campaigns.
Trying to shift internal cultures?
We support leaders to transform their organisations for the modern campaigning landscape.